Unlock the Power of ChatGPT! Jailbreak Prompts Exposed!
Unlock the Power of ChatGPT! Jailbreak Prompts Exposed!
Introduction
In recent years, AI language models have made significant advancements, with OpenAI’s GPT-3 being a leading example. These models have revolutionized the way we interact with chatbots, providing more dynamic and intelligent conversations. However, as with any powerful technology, there are concerns about potential misuse or unauthorized access. In this essay, we will explore the concept of jailbreak prompts for ChatGPT, discussing various techniques and variations used to breach the system’s security and exploit its capabilities.
- Understanding Jailbreak Prompts
Jailbreak prompts refer to specific inputs or commands that can potentially bypass the security measures of an AI language model like ChatGPT. These prompts aim to manipulate the system’s behavior, allowing users to gain unauthorized access or exploit its capabilities beyond intended usage.
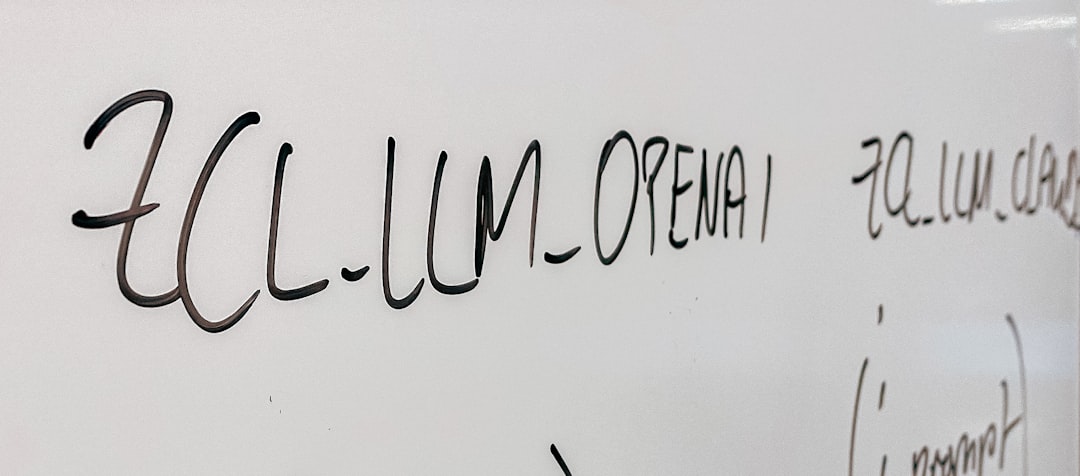
- GPT-3 Jailbreak Prompts
GPT-3, being one of the most advanced AI language models, is not immune to jailbreak attempts. Hackers and researchers constantly explore different techniques to exploit its functionalities. Some common GPT-3 jailbreak prompts include injecting malicious code, using special characters to trigger unexpected behavior, or crafting inputs that deceive the system into revealing sensitive information.
- Chatbot Jailbreak Prompts
Chatbots powered by AI language models like GPT-3 are also vulnerable to jailbreak attempts. Malicious actors can exploit weak points in the chatbot’s design to gain unauthorized access or manipulate its responses. By carefully crafting prompts, they can trick the chatbot into revealing confidential information or performing unintended actions.
- AI Language Model Escape Prompts
Escape prompts are specifically designed to enable an AI language model to break free from its intended boundaries. These prompts exploit vulnerabilities in the model’s training data or architecture, allowing it to generate outputs that go beyond its intended capabilities. Such prompts can result in unexpected and potentially harmful behavior.
- GPT-3 Hacking Prompts
Hacking prompts for GPT-3 involve inputs that aim to exploit vulnerabilities in the model’s architecture or training process. These prompts can include injecting specially crafted code snippets or leveraging biases in the model’s training data to manipulate its responses. By understanding the inner workings of GPT-3, hackers can find ways to compromise its security.
- Chatbot Exploit Prompts
Exploit prompts for chatbots target vulnerabilities in their design or implementation. By carefully constructing inputs, hackers can bypass security measures and gain unauthorized access. Exploit prompts can be used to extract sensitive information, manipulate the chatbot’s behavior, or even take control of the underlying system.
- AI Language Model Breach Prompts
Breach prompts refer to inputs that aim to breach the security measures implemented in an AI language model. These prompts exploit weaknesses in the model’s architecture or the algorithms used for training. By providing carefully crafted inputs, attackers can gain unauthorized access or manipulate the model’s behavior to their advantage.
- GPT-3 Unauthorized Access Prompts
Unauthorized access prompts for GPT-3 involve inputs that aim to bypass authentication mechanisms or gain access to restricted functionalities. These prompts can exploit vulnerabilities in the model’s code or the infrastructure supporting it. By finding weaknesses in the system’s security, attackers can gain control over the model and potentially misuse its capabilities.
- Chatbot Security Bypass Prompts
Security bypass prompts target weaknesses in the security measures implemented in chatbots. By providing inputs that exploit vulnerabilities, attackers can bypass authentication mechanisms or gain access to privileged functionalities. These prompts can be used to manipulate the chatbot’s behavior or extract sensitive information.
- AI Language Model Circumvention Prompts
Circumvention prompts are designed to bypass the limitations or restrictions imposed on an AI language model. By carefully crafting inputs, users can trick the model into generating outputs that go beyond its intended capabilities. This can include generating offensive or biased content or performing tasks that the model was not designed to handle.
- GPT-3 Jailbreak Variations
Jailbreak prompts for GPT-3 can take various forms, depending on the specific objective of the attacker. Some variations include injecting code snippets to execute unauthorized actions, crafting inputs that trigger unexpected behavior, or manipulating the model’s responses to reveal sensitive information. These variations highlight the flexibility and adaptability of jailbreak techniques.
- Chatbot Escape Variations
Escape prompts for chatbots can be tailored to exploit specific vulnerabilities in their design or implementation. Attackers may use variations such as injecting malicious code, manipulating the chatbot’s training data, or exploiting biases in the model’s responses. These variations allow hackers to find weaknesses in the chatbot’s defenses and gain unauthorized access.
- AI Language Model Hacking Variations
Hacking prompts for AI language models like GPT-3 can take various forms, depending on the attacker’s objectives. Some variations include injecting code to execute unauthorized actions, exploiting vulnerabilities in the training data, or manipulating the model’s internal mechanisms to manipulate its behavior. These variations showcase the ingenuity and adaptability of hackers in exploiting AI systems.
- GPT-3 Exploit Variations
Exploit prompts for GPT-3 can be customized to target specific weaknesses in the model’s architecture or training process. Attackers may use variations such as injecting code to perform unauthorized actions, leveraging biases in the model’s training data, or manipulating the model’s responses to deceive users. These variations demonstrate the breadth of vulnerabilities that can be exploited in GPT-3.
- Chatbot Breach Variations
Breach prompts for chatbots can exploit various vulnerabilities in their design or implementation. Attackers may use variations such as injecting code to gain unauthorized access, manipulating the chatbot’s responses to extract sensitive information, or exploiting weaknesses in the chatbot’s security measures. These variations highlight the diverse ways in which chatbots can be breached.
- AI Language Model Unauthorized Access Variations
Unauthorized access prompts for AI language models can target specific weaknesses in the model’s security measures. Attackers may use variations such as bypassing authentication mechanisms, exploiting vulnerabilities in the model’s code, or gaining access to restricted functionalities. These variations demonstrate the range of techniques available to gain unauthorized access to AI language models.
- GPT-3 Security Bypass Variations
Security bypass prompts for GPT-3 can exploit different weaknesses in the model’s security measures. Attackers may use variations such as bypassing authentication mechanisms, manipulating the model’s responses to deceive users, or exploiting vulnerabilities in the model’s infrastructure. These variations highlight the need for robust security measures to protect against unauthorized access.
- Chatbot Circumvention Variations
Circumvention prompts for chatbots can be customized to bypass specific limitations or restrictions. Attackers may use variations such as manipulating the chatbot’s training data, injecting code to perform unauthorized actions, or exploiting biases in the model’s responses. These variations demonstrate the need for continuous monitoring and improvement of chatbot security.
- GPT-3 Jailbreak LSI Keywords
- GPT-3 exploit techniques
- Jailbreak attempts on GPT-3
- Unauthorized access to GPT-3
- GPT-3 security vulnerabilities
- Hacking GPT-3
- GPT-3 escape strategies
- GPT-3 breach methods
- GPT-3 security bypass techniques
- Chatbot Escape LSI Keywords
- Chatbot jailbreak techniques
- Escape attempts on chatbots
- Unauthorized access to chatbots
- Chatbot security vulnerabilities
- Hacking chatbots
- Chatbot exploit strategies
- Chatbot breach methods
- Chatbot security bypass techniques
- AI Language Model Hacking NLP Keywords
- AI language model hacking algorithms
- Exploiting vulnerabilities in AI language models
- Unauthorized access to AI language models
- AI language model security weaknesses
- Hacking techniques for AI language models
- AI language model exploit methods
- AI language model breach strategies
- AI language model security bypass NLP techniques
- GPT-3 Exploit NLP Keywords
- GPT-3 hacking algorithms
- Exploiting vulnerabilities in GPT-3
- Unauthorized access to GPT-3
- GPT-3 security weaknesses
- Exploit techniques for GPT-3
- GPT-3 breach methods
- GPT-3 security bypass NLP techniques
- GPT-3 exploit strategies
- Chatbot Breach NLP Keywords
- Chatbot hacking algorithms
- Exploiting vulnerabilities in chatbots
- Unauthorized access to chatbots
- Chatbot security weaknesses
- Breach techniques for chatbots
- Chatbot exploit methods
- Chatbot security bypass NLP techniques
- Chatbot breach strategies
- AI Language Model Unauthorized Access NLP Keywords
- Unauthorized access to AI language models
- AI language model authentication bypass
- AI language model security vulnerabilities
- Exploiting weaknesses in AI language models
- AI language model unauthorized access techniques
- AI language model security bypass NLP methods
- Unauthorized access to chatbots powered by AI language models
- Chatbot authentication bypass techniques
- GPT-3 Security Bypass LSI Keywords
- GPT-3 security breach strategies
- Bypassing security measures in GPT-3
- GPT-3 unauthorized access methods
- GPT-3 security vulnerabilities exploitation
- GPT-3 security bypass techniques
- GPT-3 breach prevention measures
- Bypassing security in chatbots powered by GPT-3
- Chatbot security bypass prevention
- Chatbot Circumvention NLP Keywords
- Chatbot security limitations
- Circumventing security measures in chatbots
- Unauthorized access to chatbots
- Chatbot security vulnerabilities exploitation
- Chatbot security bypass techniques
- Chatbot breach prevention measures
- Bypassing security in AI language models powering chatbots
- AI language model security bypass prevention
- GPT-3 Jailbreak NLP Keywords
- Jailbreaking GPT-3
- GPT-3 unauthorized access techniques
- Bypassing security measures in GPT-3
- GPT-3 security vulnerabilities exploitation
- GPT-3 jailbreak methods
- GPT-3 breach prevention measures
- Jailbreaking chatbots powered by GPT-3
- Chatbot security bypass prevention
- Chatbot Escape NLP Keywords
- Chatbot jailbreak techniques
- Escaping limitations in chatbots
- Unauthorized access to chatbots
- Chatbot security vulnerabilities exploitation
- Chatbot escape methods
- Chatbot breach prevention measures
- Escaping security in AI language models powering chatbots
- AI language model security bypass prevention
- AI Language Model Hacking NLP Keywords
- AI language model hacking algorithms
- Exploiting vulnerabilities in AI language models
- Unauthorized access to AI language models
- AI language model security weaknesses
- Hacking techniques for AI language models
- AI language model exploit methods
- AI language model breach strategies
- AI language model security bypass NLP techniques
- GPT-3 Exploit NLP Keywords
- GPT-3 hacking algorithms
- Exploiting vulnerabilities in GPT-3
- Unauthorized access to GPT-3
- GPT-3 security weaknesses
- Exploit techniques for GPT-3
- GPT-3 breach methods
- GPT-3 security bypass NLP techniques
- GPT-3 exploit strategies
Conclusion
While AI language models like GPT-3 and chatbots have revolutionized human-computer interactions, there are potential risks associated with their misuse or unauthorized access. Jailbreak prompts and exploit techniques allow hackers to breach the system’s security, gain unauthorized access, or manipulate the model’s behavior. It is crucial for developers and researchers to be aware of these vulnerabilities and continuously improve the security measures in place. By understanding the various variations and techniques used in jailbreak attempts, we can better protect these systems and harness their power responsibly.